

Network Security
Presentation
•
Computers
•
10th Grade
•
Practice Problem
•
Easy
michaele cabatbat
Used 67+ times
FREE Resource
18 Slides • 7 Questions
1
Networking
Information and Communications Technology - 10

2
Objectives
describe the security issues that could arise from networking computers
explain how security issues can be prevented on a computer network
evaluate a range of physical and software based security methods for a computer network
3
Types of Security Issues
Unauthorized access
Malware
DoS
4
What is HACKING?

5
Open Ended

What is HACKING?
6
Unauthorized Access
hacking is unauthorized access of a computer system
once access is obtained, confidential data or sabotage of data
many techniques to gain access, most common is to find out the username and password

7
Open Ended

From what you learn before, list some techniques that a hacker can obtain a user's username and password.
8
Malware
is intrusive software that is designed to damage and destroy computers and computer systems [https://www.cisco.com]
Virus
Spyware
Trojan Horse
9
Virus
program that automatically make copies of itself to devices
usually cause damage to the files or system

10
Spyware
program designed to secretly collects information from a computer
username, passwords, credit card information etc.

11
Open Ended

What is TROJAN HORSE?
12
Trojan Horse
deleting data
blocking data
modifying data
copying data
disrupting the performance of computers or computer networks

13
Denial of Service attack
is an attack meant to shut down a machine or network, making it inaccessible to its intended users [https://www.paloaltonetworks.com]

14
How to prevent network attacks?
15

How to Prevent Network Attacks?
16
Physical Security
protecting the equipment
security guard
physical locks on the server rooms
security card etc.
17
Security Methods
access rights
biometric
firewalls
encryption
anti-virus
anti-spyware
18
Access Rights
User is assigned a set of rights to access different parts of a system
Create
Read
Update
Delete

19
Biometric
Use biological characteristics to authenticate user's identity

20
Open Ended
List some biometric authentication methods
21
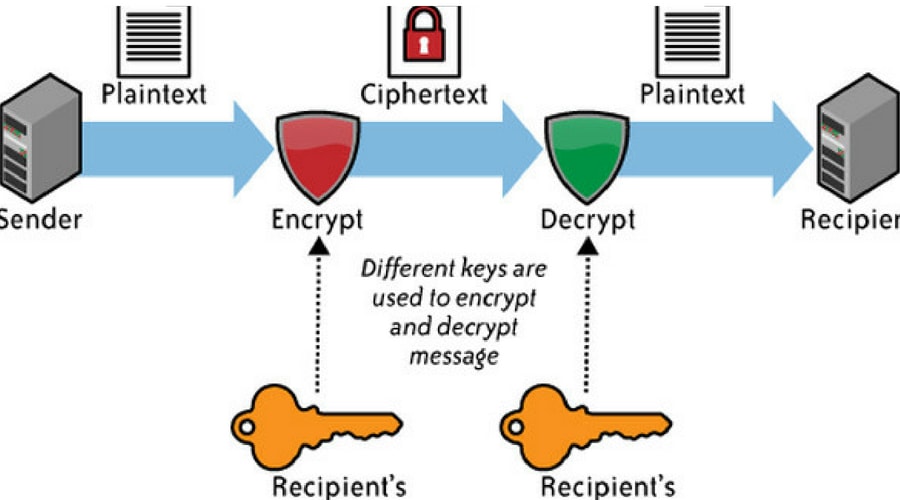
Encryption
is the process that scrambles readable text so it can only be read by the person who has the secret code, or decryption key [https://us.norton.com/]
22
Firewall
is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules [https://www.cisco.com]

23
Multiple Choice
The following are types of Network Security ISSUES, except:
unauthorized access
malware
DoS
broken router
24
Multiple Select
Select all that best describes TROJAN HORSE
acts like a bona fide application or file to trick you
a type of malicious code or software that looks legitimate but can take control of your computer
designed to damage, disrupt, steal, or in general inflict some other harmful action on your data or network
significantly disrupt your system’s performance, sapping computer memory and causing frequent computer crashes
25
Multiple Choice
These are biological measurements — or physical characteristics — that can be used to identify individuals. For example, fingerprint mapping, facial recognition, and retina scans
firewalls
biometrics
encryption
access rights
Networking
Information and Communications Technology - 10

Show answer
Auto Play
Slide 1 / 25
SLIDE
Similar Resources on Wayground

18 questions
SISTEM KOMPUTER
Presentation
•
11th Grade

22 questions
Rock-paper-scissors (microbit)
Presentation
•
9th Grade

19 questions
School Management Systems
Presentation
•
10th Grade

19 questions
ACP 1
Presentation
•
10th Grade

21 questions
Cuban Missile Crisis
Presentation
•
10th Grade

20 questions
Would You Rather?
Presentation
•
KG

20 questions
Online Essentials - Revision Lesson 1
Presentation
•
10th Grade

17 questions
Module 1 Lesson 2: Input, Output and Storage Devices
Presentation
•
10th Grade
Popular Resources on Wayground

20 questions
STAAR Review Quiz #3
Quiz
•
8th Grade

20 questions
Equivalent Fractions
Quiz
•
3rd Grade

6 questions
Marshmallow Farm Quiz
Quiz
•
2nd - 5th Grade

20 questions
Main Idea and Details
Quiz
•
5th Grade

20 questions
Context Clues
Quiz
•
6th Grade

20 questions
Inferences
Quiz
•
4th Grade

19 questions
Classifying Quadrilaterals
Quiz
•
3rd Grade

12 questions
What makes Nebraska's government unique?
Quiz
•
4th - 5th Grade
Discover more resources for Computers

50 questions
STAAR English 2 Review
Quiz
•
10th Grade

20 questions
Figurative Language Review
Quiz
•
10th Grade

20 questions
Grammar
Quiz
•
9th - 12th Grade

31 questions
Easter Trivia
Quiz
•
KG - 12th Grade

16 questions
Circles - Equations, Central & Inscribed Angles
Quiz
•
9th - 12th Grade

46 questions
Unit 4 Geosphere Test Review
Quiz
•
9th - 12th Grade

10 questions
Calculating Surface Area of a Triangular Prism
Interactive video
•
6th - 10th Grade

20 questions
Central Angles and Arc Measures 2
Quiz
•
10th Grade